You are not alone, in case you encountered the keyword bd268xz recently. This alpha numeric code has been gradually appearing in various online settings, technical forums, system logs, raising an inquiry among the developers, IT experts, digital analysts and technology enthusiasts alike. Although at a glance, it might seem to be a strange array of letters and numbers, the identifiers such as bd268xz are frequently used to perform some additional purpose in the current computing ecosystems.
In today’s hyperconnected digital environment, structured identifiers are essential for maintaining data integrity, enabling automation, improving interoperability, and scaling digital infrastructure. From backend database indexing to IoT device tracking, such identifiers play a foundational role in the invisible frameworks that support our online experiences.
This comprehensive guide explores bd268xz from multiple analytical perspectives — including potential interpretations, functional roles in technical environments, comparative identifier frameworks, performance implications, cost structures in system deployment, and future outlook in AI-driven ecosystems.
Table of Contents
What Is BD268XZ?
bd268xz is best understood as a structured alphanumeric identifier — a coded label used within software systems, digital frameworks, or hardware modules to uniquely identify, categorize, or track specific elements.
Unlike descriptive labels, identifiers like bd268xz are designed for:
- Precision in large datasets
- Machine readability
- Database indexing efficiency
- Process automation
- System-level traceability
These identifiers are commonly used in:
- Distributed computing environments
- API call tracking
- Cloud resource allocation
- IoT device authentication
- Blockchain ledger indexing
- Network configuration logs
Structured identifiers eliminate ambiguity in digital workflows by ensuring that every data entry, module, or request is mapped to a unique reference point.
Technical Foundation: How BD268XZ Functions in Digital Systems
Identifiers like bd268xz typically operate as keys in relational or non-relational databases. Their primary role is to establish a reference link between data objects and system processes.
Structural Interpretation
A breakdown of the string may resemble the following classification logic:
| Segment | Hypothetical Role |
| BD | Project type or system classification |
| 268 | Batch or sequence number |
| XZ | Version marker or deployment region |
Such segmentation allows systems to interpret identifiers programmatically — improving indexing speed and minimizing collision risk in large-scale deployments.
Operational Roles
Within a computing environment, bd268xz-type identifiers may be used for:
- Resource tagging in cloud platforms
- Event logging in distributed systems
- Firmware identification in embedded devices
- Configuration mapping in network environments
- Security tokenization for encrypted sessions
Core Features & Capabilities of Structured Identifiers Like BD268XZ
When implemented correctly, identifiers such as bd268xz provide several performance-enhancing characteristics:
Key Functional Advantages
- High Uniqueness Ratio
Minimizes duplication across large datasets. - Machine-Level Processing
Compatible with automated workflows and scripting environments. - System Scalability
Supports expansion into multi-node architectures. - Interoperability
Integrates across cloud services, APIs, and network layers. - Security Compatibility
Can be hashed or encrypted for secure data exchange.
These capabilities make structured identifiers indispensable in environments where operational accuracy and performance efficiency are critical.
Real-World Use Cases
Software Development Pipelines
Development frameworks rely heavily on identifier strings for:
- Build tracking
- Version tagging
- Dependency mapping
- Error log correlation
CI/CD systems often generate unique IDs similar to bd268xz for every deployment instance.
Cloud Infrastructure Management
Cloud platforms allocate unique resource IDs to:
- Virtual machines
- Storage buckets
- Serverless functions
- Containerized workloads
These identifiers allow orchestration engines to dynamically route processes across distributed environments.
IoT Networks
Connected devices in IoT ecosystems require unique identification to:
- Authenticate network access
- Track telemetry data
- Manage firmware updates
- Optimize energy consumption
Identifiers enable real-time communication across billions of interconnected nodes.
Logistics & Inventory Systems
Digital supply chain platforms utilize identifier strings to monitor:
- Product lifecycle
- Batch traceability
- Shipment routing
- Warranty validation
This ensures transparency and accountability in global distribution networks.
Cybersecurity Frameworks
Identifiers may function as:
- Session tokens
- Access credentials
- Audit trail markers
- Encryption references
Security protocols often generate temporary identifiers to verify user authenticity during transactions.
Cost Implications in System Deployment
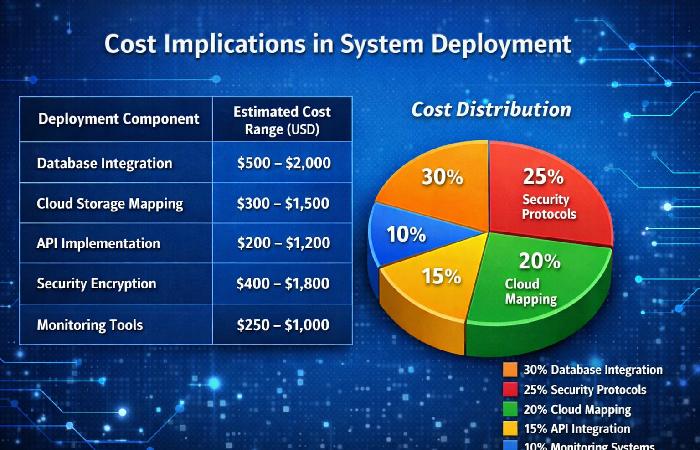
Deploying identifier frameworks like bd268xz within enterprise environments can have measurable cost impacts.
Infrastructure Cost Breakdown
| Deployment Component | Estimated Cost Range (USD) |
| Database Integration | $500 – $2000 |
| Cloud Storage Mapping | $300 – $1500 |
| API Implementation | $200 – $1200 |
| Security Encryption | $400 – $1800 |
| Monitoring Tools | $250 – $1000 |
Cost Distribution (Pie Representation)
- Database Integration: 30%
- Security Protocols: 25%
- Cloud Mapping: 20%
- API Integration: 15%
- Monitoring Systems: 10%
Understanding these cost allocations can help organizations optimize deployment budgets and scalability strategies.
Comparison with Other Identifier Systems
| Feature | BD268XZ-Type Code | UUID | MAC Address | Semantic Version |
| Uniqueness | High | Very High | High | Medium |
| Readability | Low | Very Low | Medium | High |
| Security Integration | Possible | Strong | Limited | None |
| Scalability | High | Excellent | Medium | Medium |
| Collision Risk | Moderate | Minimal | Low | N/A |
UUIDs may offer stronger uniqueness guarantees, but shorter identifiers like bd268xz can improve processing speed and storage efficiency. (Oracle)
Challenges and Limitations
While structured identifiers offer numerous advantages, they also present certain operational challenges:
- Human readability limitations
- Potential metadata dependency
- Typographical entry errors
- System parsing inconsistencies
- Collision risk in poorly designed frameworks
Implementing validation protocols can mitigate many of these issues.
Best Practices for Managing Identifier Frameworks

Organizations deploying identifier systems should consider:
- Maintaining centralized metadata repositories
- Enforcing input validation rules
- Implementing encryption standards
- Enabling version history tracking
- Conducting periodic collision audits
Adhering to governance policies ensures system reliability and long-term scalability.
Integration with Emerging Technologies
As digital ecosystems evolve, identifiers like bd268xz may become increasingly integrated with:
- AI-driven automation systems
- Blockchain asset registries
- Edge computing nodes
- Smart city infrastructure
- Autonomous vehicle networks
Self-describing identifiers — embedded with contextual metadata — could significantly enhance system intelligence and predictive analytics capabilities.
Performance Optimization Strategies
To improve identifier efficiency:
- Use hash-based generation algorithms
- Minimize string length without sacrificing uniqueness
- Implement distributed indexing
- Enable real-time collision detection
- Optimize database schema design
These strategies can reduce processing latency and improve overall system throughput.
Future Outlook
The demand for scalable identification mechanisms will grow alongside:
- IoT expansion
- AI-driven analytics
- Decentralized financial networks
- Quantum computing frameworks
- Cloud-native application architectures
Identifiers will continue serving as the foundational layer that enables synchronization across increasingly complex digital ecosystems. (Cloudfare)
Summary and Key Takeaways
| Insight Area | Core Observation |
| Definition | bd268xz is a structured alphanumeric identifier. |
| Functionality | Enables precise tracking and system automation. |
| Applications | Software, IoT, cloud, logistics, cybersecurity. |
| Cost Factors | Deployment costs vary by infrastructure layer. |
| Best Practices | Validation, encryption, governance. |
| Future Role | Critical for AI and distributed networks. |
Conclusion
Identifiers can be seen as mere at first glance but they are the foundation of contemporary computing environments. Systems need to be built on organised identifiers such as bd268xz whether managing data pipelines, device authentication, or distributed workloads, to ensure the accuracy, scalability and continuity of operations.